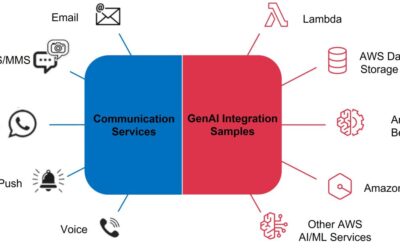
Your customers reach out through SMS. Through email. Through WhatsApp. Through web chat.
Your team responds through… spreadsheets? Disconnected inboxes? Maybe a CRM that sort of ties things together?
Meanwhile, each channel has its own queue, its own response time, its own tribal knowledge about how to handle common questions. Customer context gets lost between channels. Response quality varies wildly depending on who’s working.
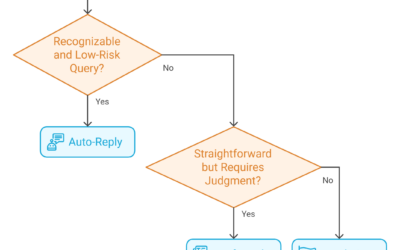
There’s a better way. Amazon Bedrock—combined with AWS End User Messaging and SES—enables enterprises to build unified communication hubs where AI handles routine inquiries across every channel, escalates complex issues to humans, and maintains full context throughout the customer journey.